With a well-tought security system, Frank keeps data safely available.
With a combination of tools and information classification, you can easily manage access to sensitive information.
1. Introduction
With a combination of tools and information classification, you can easily manage access to sensitive information.
Frank manages security with a role based system. Each Position in your company has a set of security-keys wich defines the features that can access.
So, when you assign staff to a Position, the person inherits the role permissions.
Frank also classifies the information in two groups, Public and Classified, to easily identify the type of information you're seeing or allowing to access.
On the following sections we will explain all this concepts.
2. Information Classification
| Public information | Everything that's not classified |
| Classified information | This is sensitive data as financial information, salaries, etc. To easily identify this type of information, you'll see that the screen turns dark grey in sections that contains classified information. |
3. Permissions & Security Keys
Access to information is managed through Permissions. Each permission grant access to a Frank feature, including modules, sub-modules, objects, and object sections.
A Security Key is a combination or group of permissions, that you can assign to Users or Positions.
To manage security-keys, access the following link:
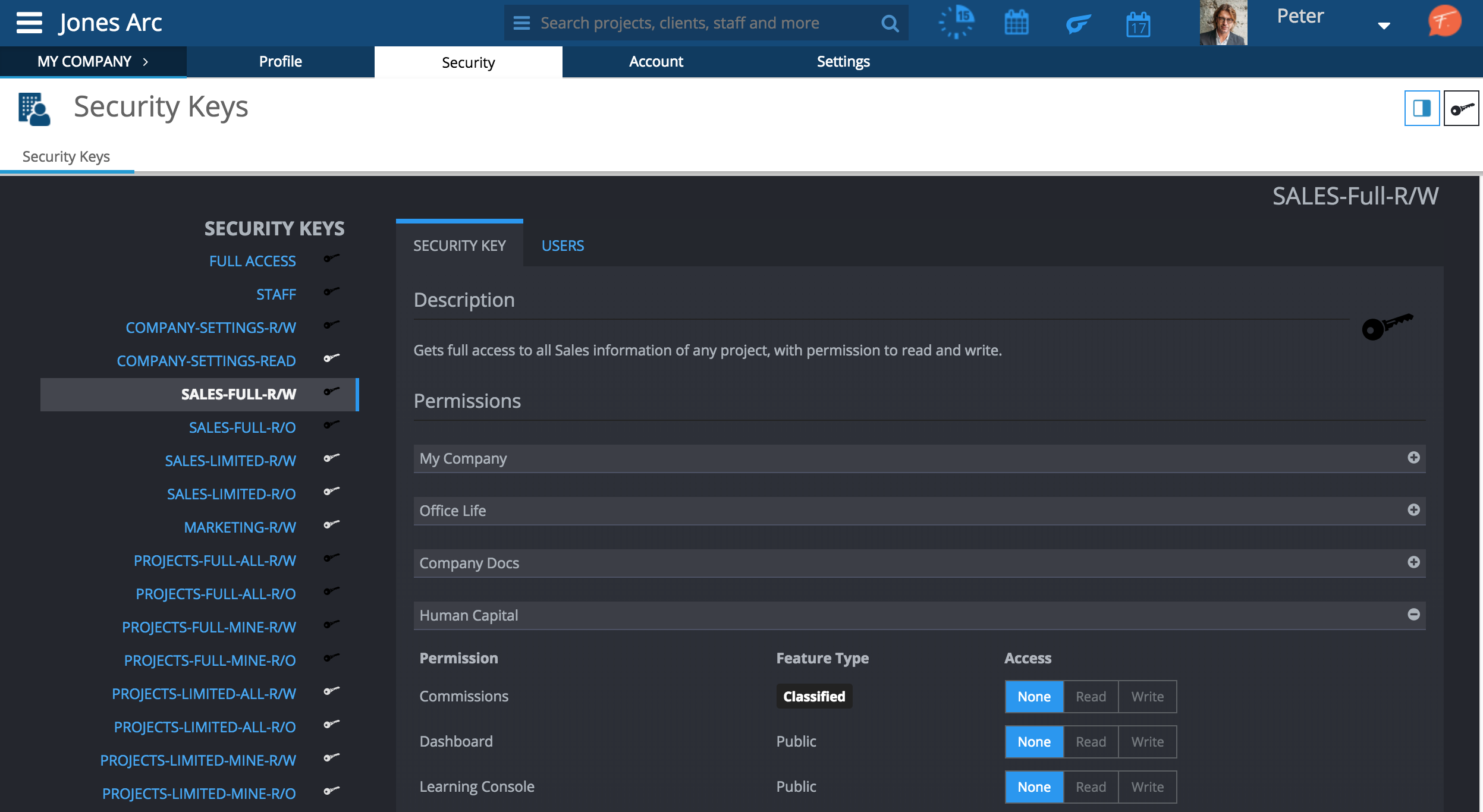
On the left of the screen you'll see all the built-in security keys. When you click on one of them, two tabs are enabled:
1. Security Key: contains the detail of the permissions that this security key has.2. Users: contains the Users from your staff that have this security key. From this tab you can add/remove users.
4. Positions
The preferred way to manage security is through the use of Positions. Once you've defined your company Positions, you can assign them one or more security-keys based on the rol of users in the company.
So, when you assign a staff to a Position, the person inherits the permissions that the position has.
To manage Positions, please access the following link:
ADMINISTRATION > HUMAN CAPITAL > POSITIONS
Each Position has a section named "Security Keys", where you can add or remove security keys. Each security key has a set of permissions that will be granted to the Staff assigned to the position.
To check the resulting permission set for a specific position, click on the button "Permissions Summary" at the bottom of the section. This will show all the effective permissions that the position has.
5. Checking access to information
To check the effective permissions for a user, access the Permissions window from the Staff Profile.
To check the required permissions for a particular feature (screen), click on the key button on the top-right corner.